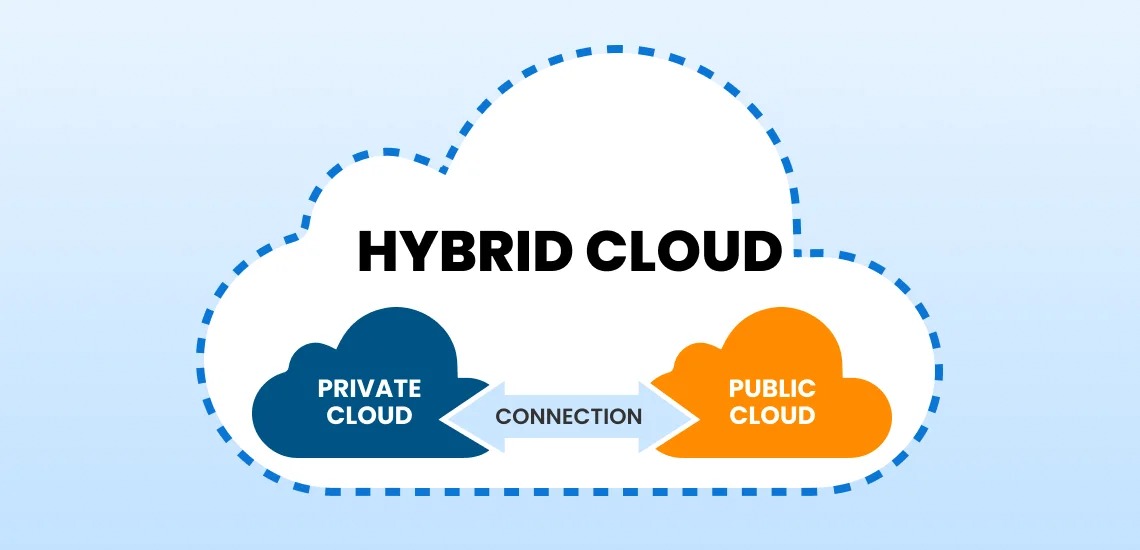
Moving data between private servers and public clouds feels like a high-stakes balancing act. You want the speed of the modern web, but you need the tight security of a locked vault. This mix is what we call a hybrid cloud. It gives your business the best of both worlds by spreading tasks across different spaces. Many companies worry about hackers or leaked files when they move to the cloud. You do not have to choose between innovation and safety anymore. New tools allow you to keep your most private files on your own hardware while using the cloud for everything else. This setup keeps your team fast and your customers safe. Learning these methods will change how you view digital security forever. Let us dive into the best ways to manage this balance.
1. Lock Your Data In A Digital Vault
The first step focuses on keeping the crown jewels off the public internet. You store highly sensitive records on a private server that you own and control. This physical control means you decide exactly who sees the files at all times. You then connect this server to a public cloud for basic tasks like sending emails or hosting a website. This bridge allows data to flow without exposing the main database to the open web. Your Hybrid Cloud computing environment keeps critical data protected on private infrastructure while still using the public cloud for scalable everyday workloads.
Managing Your Secret Keys
You should hold the digital keys to your data yourself. Do not let the cloud provider manage your locks. This gives you total power over your digital kingdom.
Once you lock the doors with encryption, you must think about how the data actually travels.
2. Build A Private Road For Your Information
Standard internet connections are often messy and crowded like a busy highway. You can bypass this chaos by setting up a dedicated network link. This acts as a private road built just for your company. No other traffic can jump on this path while your data moves. It lowers the risk of someone intercepting your files mid-stream. This private path also makes your connection much faster and more reliable. You get consistent speeds because you do not share the lane with anyone else.
Watching Every Single Move
You need tools that track every person who enters your network. Real-time alerts tell you if a stranger tries to open a file. This constant watching keeps your private road secure from intruders.
Scaling Up Without Giving Up Control
A private road lets you grow your business quickly. You can add more data capacity without rebuilding your entire security wall.
3. Slice Your Network Into Tiny Safety Zones
Imagine your cloud environment as a building that contains multiple separate spaces. The practice of network segmentation requires you to install locks on all entrance points throughout your network. If a thief gets into the lobby, they still cannot reach the back office. You group your sensitive data into its own tiny digital island. This island stays away from the general parts of your cloud. It prevents a small problem in one area from becoming a total disaster. You gain much more control over internal movement this way.
Using Firewalls Between Every Slice
Digital firewalls act as guards at every single door. They check the ID of every bit of data trying to pass through. This keeps your segments clean and safe from bad software.
Automating Your Security Checks
Computers can scan these segments much faster than humans can. Automated tools find weak spots before a hacker even knows they exist.
4. Hide Your Identity With Smart Masking
Data masking replaces your real information with fake but functional data. Imagine a credit card number where the middle digits are all zeros. This allows your team to test software without seeing real customer details. The real data stays hidden in your private vault at all times. Only the fake version travels into the public cloud for work. This lowers the chance of a leak during daily operations. Your employees can do their jobs perfectly without ever touching a sensitive file.
5. Keep Your Compliance Rules In One Place
The GDPR and HIPAA laws demand that you follow their strict regulations. A hybrid cloud computing network enables you to comply with these requirements because it stores regulated data at your location. You use the public cloud to process the data, but never to store it long term. This strategy keeps the government happy and your fines at zero. You can generate reports that prove you are following every single law. It simplifies the job for your legal team and your tech team.
6. Distribute Your Tasks To Lower The Risk
You should never put all your eggs in one basket. Splitting your workload across two different cloud providers adds an extra layer of safety. If one provider has a security flaw, your other half stays safe. This strategy forces you to stay organized and keeps your data mobile. You avoid getting stuck with one vendor who might raise prices or lower security. It creates a competitive environment that favors your privacy.
7. Use Edge Computing For Local Privacy
Edge computing processes data at the location of its generation. A camera serves as an example because it performs video analysis directly on the device without sending the footage to cloud storage. This means the raw and sensitive footage never leaves the building. Only a small summary of the data goes to the hybrid cloud. This keeps the most detailed information local and private. It reduces the amount of data traveling over the web significantly.
8. Create A Unified Security Command Center
You need a single screen to watch your entire hybrid world. A unified dashboard shows you the health of both your private and public clouds. This bird’s eye view helps you spot patterns that look suspicious. You can shut down a threat in seconds across your whole network. Managing everything from one spot reduces human error and missed alerts. It brings peace of mind to your entire IT department.
Conclusion
Securing a hybrid cloud does not have to be a scary mystery. You simply need the right mix of private storage and smart public tools. By using private roads and masked data, you build a fortress that still moves fast. These eight steps give you a clear map to follow for a safer digital future. You can now grow your business with total confidence in your security. Your data stays yours while the cloud does the heavy lifting. This balance is the ultimate goal for any modern company.